How To Check Event Log In Windows Server 2016
Hello,
It has been a while since Raven, and I have blogged on security. My piffling buddy Raven (miniature Schnauzer) has been dealing with genetic dorsum problems that have made it difficult to run or jump, so her days of roaming the one thousand and scaring off squirrels has been curtailed.
This past summertime I was able to spend a lot of fourth dimension in my backyard with Raven quietly resting aslope me. Raven has never given upwardly on protecting the yard, only she needs help from me to find the intruders. She lays there quietly simply when I say "Squirrel" and point, her back problems vanish temporarily as she vanquishes the little critter (don't worry she never gets close to ane).
As I initially sat and work on the technical topic of this web log, it dawned on me how much Raven needing help finding intruders and what Microsoft Sentinel (Formerly Azure Scout) tin can provide to our customers. Microsoft Sentinel is the alerting machinery that finds the anomalies in your environment and can warning you lot to get evict them.
Windows Event Forwarding (WEF) isn't something new, I believe information technology has been around for more than 20 years, but the ability to query has never been its strong indicate, plus storage can be an issue. Having the ability to get access to all of the enterprises Windows Event logging data without having to load a customer (WEF is built into the o/southward) has two major advantages.
No cost
No agent direction
Imagine a customer with close to 200,000 endpoints and having to maintain the installed customer base, that could be a real headache and client costs are very high (I am working with such a scenario). A WEC server tin can't have that large of a number of clients then it has to be split out, and I take been asked "how many clients could connect to a single WEC server?" There is no precise answer to that question. Since there are many factors that enter into that question. Size of WEC server, amount of traffic being sent,… I have seen that the number of a clients that a WEC server can handle, could go as high equally 10,000 clients but again the surround factors enter into this.
One time one or more WEC server have been stood up and then yous volition need to add together an "Azure Arc" connection to Azure, so Microsoft Sentinel can "Connect" to the WEC server. The Microsoft Watch connector "Windows Forwarded Events (Preview)" requires AMA, equally information technology is not supported for MMA, and AMA requires the deployment of Azure Arc.
This will and then provide the customer complete access to the logs from the hosts that exist outside of Azure (On-Premises, AWS, GCP for example) that were aggregated with WEF.
Below I take walked through the steps needed to help deploy a WEF to Microsoft Lookout infrastructure.
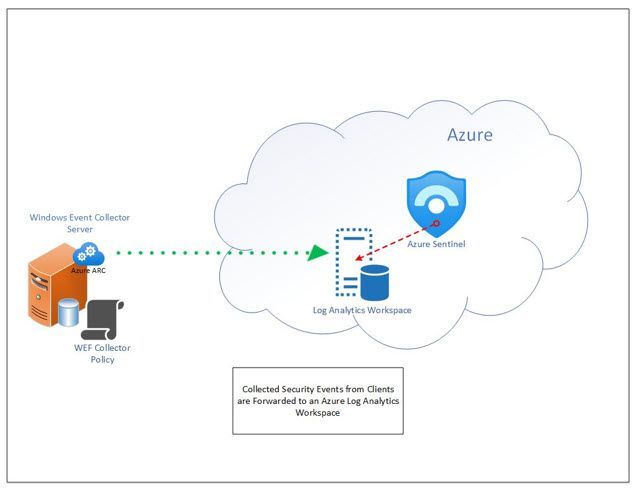
There is no need to load an agent on every device to capture the Windows Security Event Logs from your on-premises Windows workstations & servers. Windows hosts already have this built into the operating organization. To capture the events without having to load the Azure Monitoring Agent (AMA) the Windows Event Forwarding process can be used to send logs to a "Windows Event Collector" (WEC). The WEC will then demand the AMA loaded to send the events to a Log Analytics Workspace (LAW) that is monitored past Microsoft Sentinel.
Note: Microsoft Sentinel must be enabled/deployed prior to the deployment of the AMA agent.
From a high-altitude view:
- Deploy Microsoft Sentinel
- Build a Windows Event Collector (WEC) server to host the security result logs from client (source) computers
- Create a Grouping Policy to define where the clients are to asking the logs and events (Subscription), they are to send to the WEC
- Create a subscription on the WEC to define what logs and events to receive
- For on-premises WEC server(s), enroll it/them in the Azure Arc service
- Add the Microsoft Sentry, "Windows Forwarded Events (Preview)" connector
- Define the WEC hosts
- Define the "Forwarding Outcome Logs" log to collect from
- Browse/Query (KQL) the LAW for Security Events
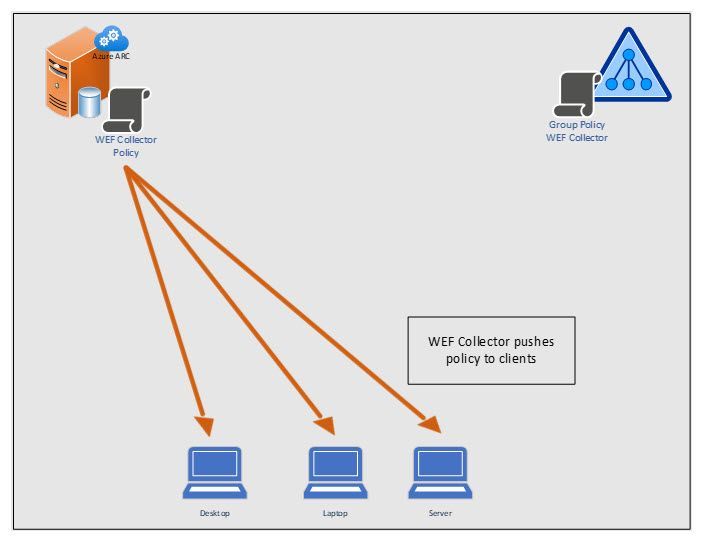
Create and Push GPO To Clients So They Tin Find the WEF Collector

Clients Asking WEF Policy from WEF Server

WEF Collector Pushes Policy to Clients
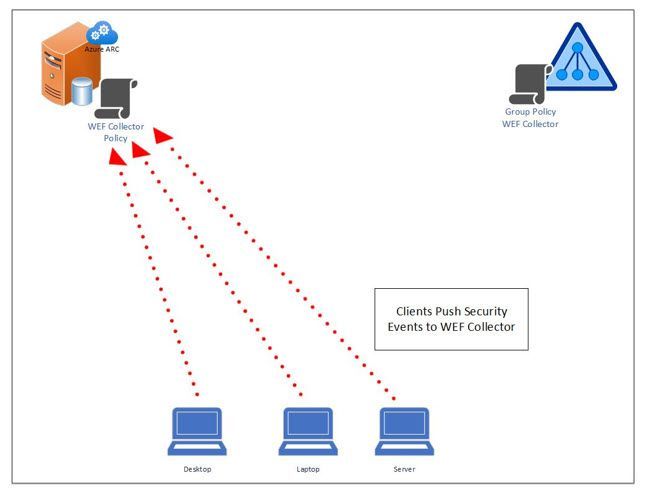
Clients Continuously Button Security Events to WEF Collector
Collected Security Events are Continuously Forwarded to the Azure Log Analytics Workspace
This is a resource requirement. The size of the host will depend on the number of source clients and logs being forwarded to the WEC.
"You deploy EventLog Forwarding in a big surroundings. For example, you deploy twoscore,000 to 100,000 source computers. In this situation, nosotros recommend that you deploy more one collector that has 2,000 clients to not more than than 4,000 clients per collector.
Note: AMA tin handle up to 5,000 EPS, merely be aware that it is important to accept enough WEC servers as if the limit of EPS is reached the agent won't exist able to handle the load.
Additionally, we recommend that you install at least 16 GB of RAM and four (4) processors on the collector to support an average load of ii,000 to 4,000 clients that accept 1 or two subscriptions configured.
Fast disks are recommended, and the ForwardedEvents log can be put onto another disk for better performance.
The memory usage of the Windows Effect Collector service depends on the number of connections that are received past the client. The number of connections depends on the following factors:
- The frequency of the connections
- The number of subscriptions
- The number of clients
- The operating arrangement of the clients
For example, for the default values of 4,000 clients and five to seven subscriptions, the memory that is used by the Windows Event Collector service may quickly exceed 4 GB and continue to grow. This can brand the calculator unresponsive."
Best practice of configuring EventLog forwarding functioning - Windows Server | Microsoft Docs
Ensure Events tin can be forwarded if running on a Windows Server
"Symptoms
You configure a Windows Server 2019 or Windows Server 2016 reckoner as an event collector. Y'all also configure a source-initiated subscription (and related Group Policy Objects) for effect forwarding. However, the events are not forwarded and the event source computers log outcome letters that resemble the following:
Log Name: Microsoft-Windows-Forwarding/Operational
Event ID: 105
Job Category: None
User: NETWORK SERVICE
Description:
The forwarder is having a problem communicating with subscription manager at address http://W19SRV.contoso.com:5985/wsman/SubscriptionManager/WEC. Error code is 2150859027 and Error Message is The WinRM client sent a request to an HTTP server and got a response maxim the requested HTTP URL was not available. This is normally returned by a HTTP server that does non support the WS-Direction protocol.
This behavior is caused by the permissions that are configured for the following URLs:
- http://+:5985/wsman/
- http://+:5986/wsman/
On the result collector figurer, both the Windows Event Collector service (WecSvc) and the Windows Remote Management service (WinRM) use these URLs. However, the default admission control lists (ACLs) for these URLs allow access for only the svchost process that runs WinRM. In the default configuration of Windows Server 2016, a single svchost process runs both WinRM and WecSvc. Considering the procedure has admission, both services office correctly. However, if you lot alter the configuration and so that the services run on dissever host processes, WecSvc no longer has admission and outcome forwarding no longer functions.
To view the URL permissions, open up an elevated Command Prompt window and run the command netsh http show urlacl.
To prepare the URL permissions, utilise the elevated Command Prompt window and run the following commands:
netsh http delete urlacl url=http://+:5985/wsman/
netsh http add urlacl url=http://+:5985/wsman/ sddl=D:(A;;GX;;;S-i-5-fourscore-569256582-2953403351-2909559716-1301513147-412116970)(A;;GX;;;S-ane-5-80-4059739203-877974739-1245631912-527174227-2996563517)
netsh http delete urlacl url=https://+:5986/wsman/
netsh http add urlacl url=https://+:5986/wsman/ sddl=D:(A;;GX;;;Southward-one-v-80-569256582-2953403351-2909559716-1301513147-412116970)(A;;GX;;;S-1-v-80-4059739203-877974739-1245631912-527174227-2996563517)"
Outcome collector doesn't forwards events - Windows Server | Microsoft Docs
WEF uses WINRM, which uses ports 5985 for http or 5986 for https. Ensure that you lot have the winrm service running on clients before you first capturing traffic. Winrm is started by default on Windows Server 2008 and beyond.
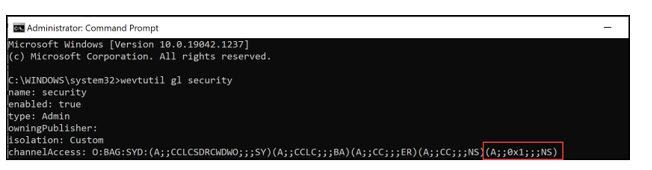
If the goal is to capture the Security effect logs as one of the logs (In our demo we will demand to capture the Security Event Logs), then information technology will be required to grant the "Network Service" access to the Security issue log, by default access is denied. From an Active Directory domain machine, run the post-obit command, from an elevated command line:
wevtutil gl security
This will list out the ACL's defined on the Security Event Log. Look for "channelAccess" the "O:BAG:SYD:" is where the permissions on the log are stored. Copy from the O through the last parenthesis and paste it into Notepad. If there isn't a (A;;0x1;;;NS) on the end like the example below, and so append that on to the line in Notepad. This concluding part provides the Network Service (NS), access to the Security Effect log.
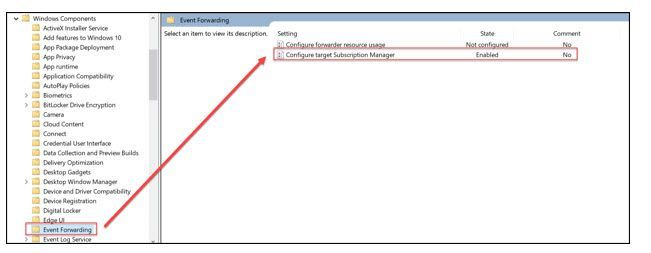
Get-go upwards Group Policy Management Editor
In that location are 2 settings that will need to be added, to point the clients to the WEC server
Figurer>Policies>Admin Templates>Windows Components>Event Forwarding>Configure target subscription manager
This volition need to be updated with the address of your WEC server in the format shown below:
Server=http:// fqdnofWECserver :5985/wsman/SubscriptionManager/WEC,Refresh=60
Supplant the blood-red highlighted area with the fqdn of the WEC server.
Note: "Server=" is needed in the line defined higher up
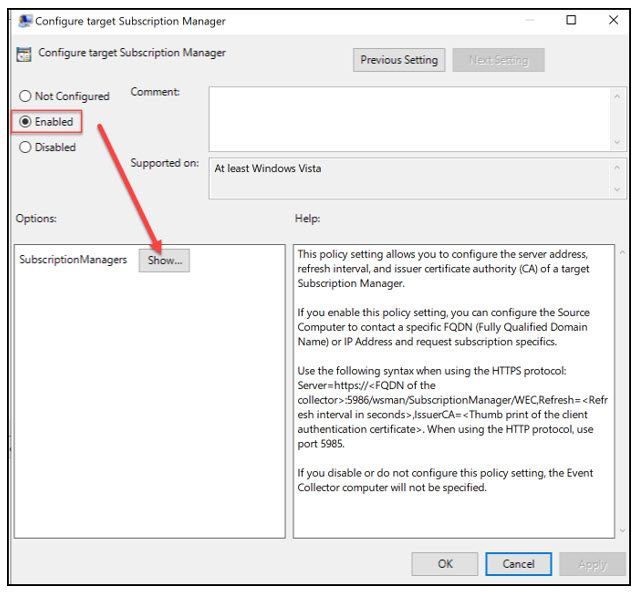
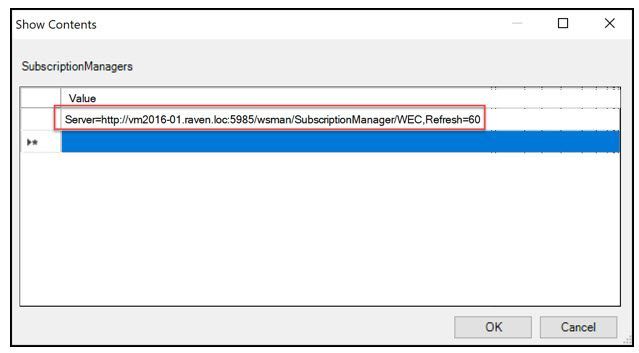
The refresh interval on the end indicates how often clients should check in to see if new subscriptions are available. In this example 60 seconds is extremely chatty, simply during testing y'all simply have to wait 1 minute for updated configuration. Setting to hourly (Refresh=3600) in production should work just fine.
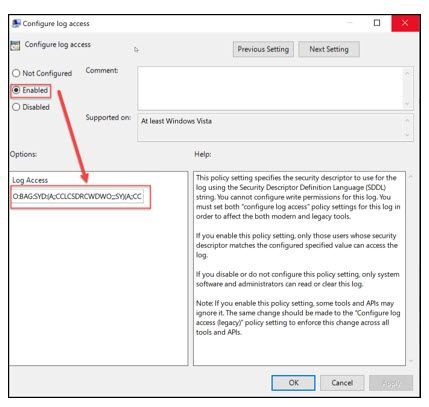
Once the defined WEC has been completed, the Network Service needs to be granted access to the Security Consequence Log. This step is not needed if you won't be reading that log file.
Computer>Policies>Admin Templates>Windows Components>Effect Log Service>Security> Configure log access
From a previous step where the Security Event log permissions were built and stored in Notepad, this value will now be updated in the GPO.
Note: This will replace any previous settings on this Event Log, so just be aware of this update.

In one case this GPO has been built, it volition exist up to the admin to make up one's mind how to apply the policy to the workstations/servers so they can check in with the WEC server to go the subscription definition.
At present that client GPO has been defined a subscription needs to be built to tell these clients what logs and Events should be "Forwarded".
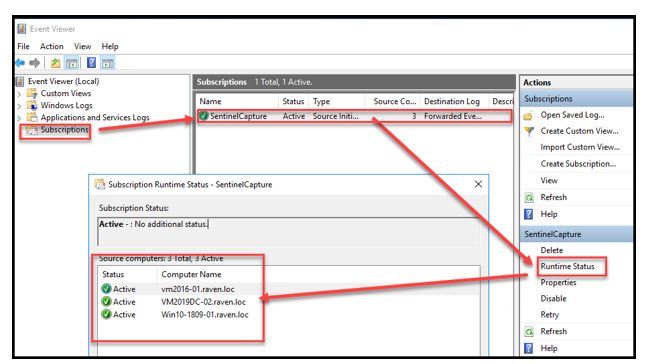
From the WEC server, start up "Event Viewer".

Right click on "Subscriptions" and select "Create Subscription...".
- "Subscription name:" Enter a unique name for the subscription (endeavor to avert spaces)
- "Description:" is optional
- "Destination log:" Select the log file "Forwarded Events"
- Select "Source Reckoner Initiated"
- Click on "Select Estimator Groups…"

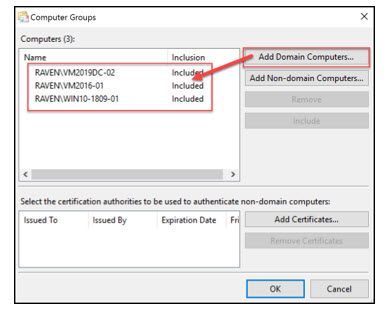
Select the "Add together Domain Computers" button and walk through the Active Directory (Advertizing) picker to populate the Computers to exist added. In the example below, there are just individual machines merely AD groups can also be used. Once all objects have been selected click the "Ok" push button"
From the "Subscription Properties" main page, click on the "Select events" button.
The "Query Filter" page allows the admin of the filter the ability to only forward events interested in capturing. This filter will be used by all client subscribers that are forwarding events. These events will all be sent to the WEC server. If the admin would like the WEC server to capture all events but filter this list before sending to Microsoft Sentinel, there is a second filter definition on the Microsoft Sentry connector.
Notation: Events are continuously sent to the WEF collector
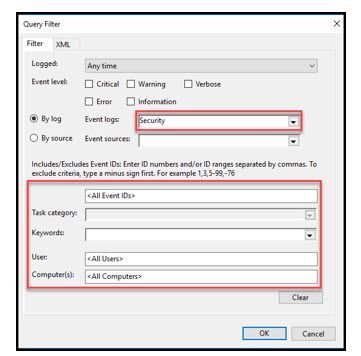
Once filtering has been completed, select "Ok" and select "Ok" once again on the Subscription properties page.
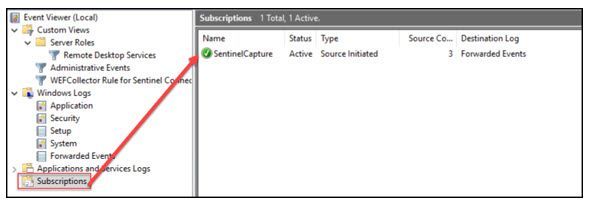
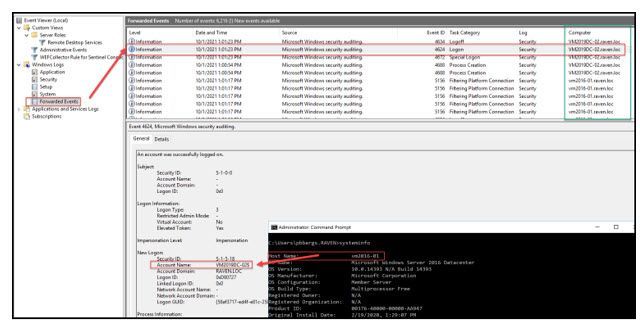
Waiting approximately fifteen minutes (Afterwards the GPO has applied to the clients), the "Forwarded Events" log should brainstorm to populate from subscribers to the WEC subscription.
If you look closely at the screen capture below you volition see that the "Forwarded Events" log resides on vm2016-01 (DOS prompt), yet the reporting in the consequence itself belongs to VM2019DC-01.
In order to capture events within Microsoft Spotter, there has to be a connection to the Log Analytics workspace that Microsoft Sentinel monitors. To exercise this we need to enroll our WEC server into Azure Arc. This is completed past installing the Azure Monitor Amanuensis.
- Log onto the Azure portal:
https://portal.azure.com - From the search portal enter, "Servers - Azure Arc" and select this to go to the "Servers - Azure Arc" bract.
- Click on "+ Add"

- For this initial trial rollout, select the "Generate Script" from the "Add a unmarried server" box.
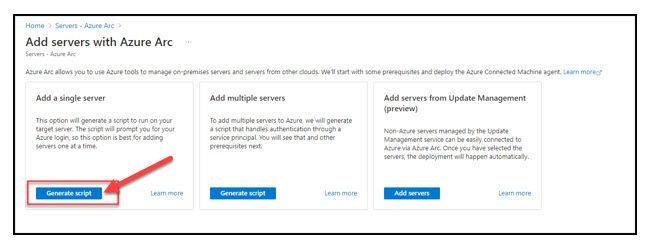
- Select "Next"
- Complete the Resources Details and click on "Adjacent"
Notation: In the case from my lab below, I am using a "Public" endpoint. I would strongly encourage organizations to not expose ANY log files on the public cyberspace!

- Enter any required "Tags" for your organization and select "Next"
- Select the "Download" button
- Select the "Copy" push button
- The "Download" button will probably exist blocked by your organization

- From the on-premises WEC collector desktop, open a script editor (Notepad for example) and paste the contents of the clipboard and save it as "WEC-Sentry.ps1".
- Open up an elevated PowerShell command prompt
- Modify directories to where you saved "WEC-Sentinel.ps1"
- Execute the script: .\WEC-Lookout.ps1

- You volition be prompted to sign into a web browser and enter a code

- Follow the on screen prompts to logon and corroborate the joining of this machine to Azure Arc

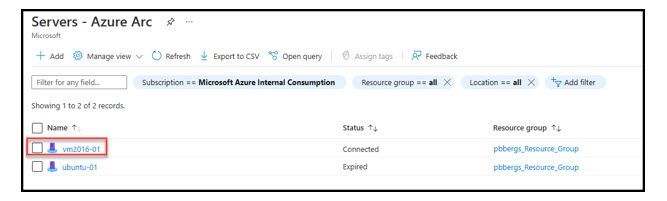
- Motility back to the "Servers – Azure Arc" blade, hit refresh and the newly onboarded host should now exist a part of this subscriptions "Azure Arc" as seen with the Data Collector ("vm2016-01") beneath.
Once events are being nerveless, the events now need to be imported into a "Log Analytics Workspace" (LAW) for Sentinel to be able to monitor and report on them.
- Log onto the Azure portal:
https://portal.azure.com - Select Microsoft Sentinel

- Select the "Data Connectors" blade
- Select the Law that you would like to aggregate events to from the WEC

- Enter "Windows Forwarded Events" in the "Search past name or provider" box
- Click on "Windows Forwarded Result"
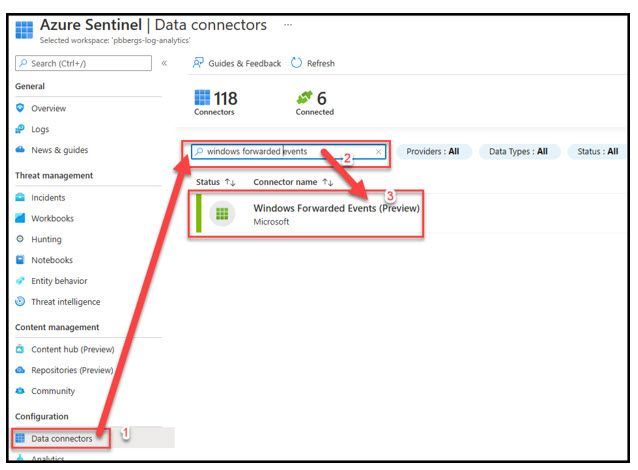
- Select "Open up connector folio"

- Select "+Add information collection rule"

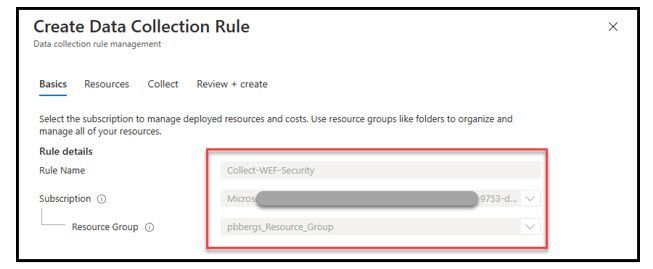
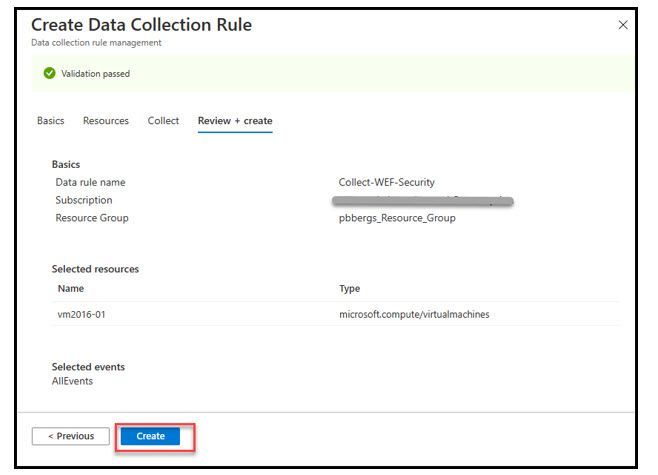
- On the "Basics" tab enter
- "Rule Name", "Subscription" and "Resource Group"
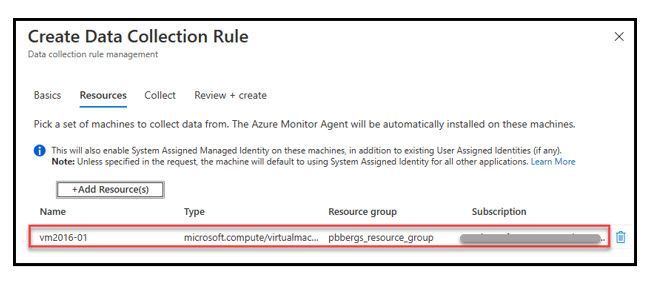
- On the "Resources" select the "+Add Resource(s)"

- Scan to the "Collector(s)" that will be capturing on-premises Security upshot logs
- Click the "Apply" push button

- On the "Collect" tab select the "+Add Resources(s)"
- Scan to the on-premises Data Collector (VM2016-01)
- Select the "Utilize" push
- Choose if you desire to transport ALL security events or but a filtered list
- Click the "Next" button

- Click the "Create" button

- Log onto the Azure portal:
https://portal.azure.com - Select Azure Sentinel
- Select the LAW
- Select the "Logs" blade
- Close the "Favorites" query folio

- To query the WEF logs imported into Microsoft Lookout, the ambassador can open a KQL query with the "WindowsEvent" tabular array
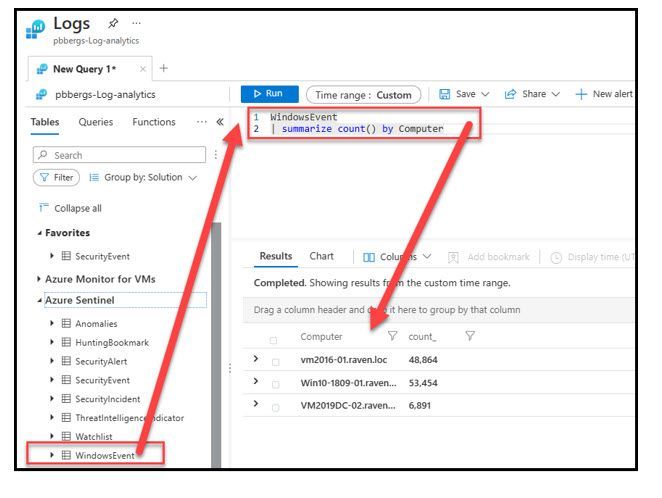
- At that place are 3 hosts that are currently reporting to my LAW, which is defined within the WEC subscription(s)
- VM2016-01
- Win10-1809-01
- WV2019DC-02
This document won't dive any deeper into KQL, if that is needed a carve up document tin can be built to assist with filtering.
Hopefully this has provided you with some options to reduce costs and get your log data in a SIEM. I know Raven really appreciates me "Alerting" her to intruders in the backyard. :smiling_face_with_smiling_eyes:
- Windows Event Forwarding: Survival Guide - TechNet Manufactures - United States (English) - TechNet Wiki...
- Setting upward a Source Initiated Subscription - Win32 apps | Microsoft Docs
- Best practice of configuring EventLog forwarding functioning - Windows Server | Microsoft Docs
- Employ Windows Event Forwarding to help with intrusion detection (Windows 10) - Windows security | Micr...
- Azure Arc overview - Azure Arc | Microsoft Docs
-
Event collector doesn't forward events - Windows Server | Microsoft Docs
Source: https://techcommunity.microsoft.com/t5/core-infrastructure-and-security/forward-on-premises-windows-security-event-logs-to-microsoft/ba-p/3040784
Posted by: burnsbountly.blogspot.com

0 Response to "How To Check Event Log In Windows Server 2016"
Post a Comment